2FA Bypass Vulnerability Allowing me to Access Victim Accounts Without 2FA Code
Author: Amine SAJID
Introduction
During a security assessment of a public program, I discovered a 2FA bypass vulnerability that allows attackers to bypass the two-factor authentication (2FA) mechanism by exploiting the “Linked Accounts” function. This vulnerability allows attackers to switch between user accounts without requiring a 2FA code, leading to unauthorized access.
Bug Type: 2FA Bypass
Impact: Unauthorized Account Access, Security Bypass
Severity: Medium
The Hunt Begins
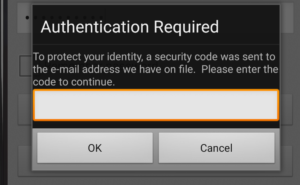
After logging in, I was prompted for a 2FA code to access my account. I tried several techniques to bypass the 2FA, such as:
- Entering
000000as the code. - Checking if the 2FA code was leaked in the response.
- Testing if another user’s 2FA code would work.
- Attempting to access dashboard endpoints without entering the 2FA code…
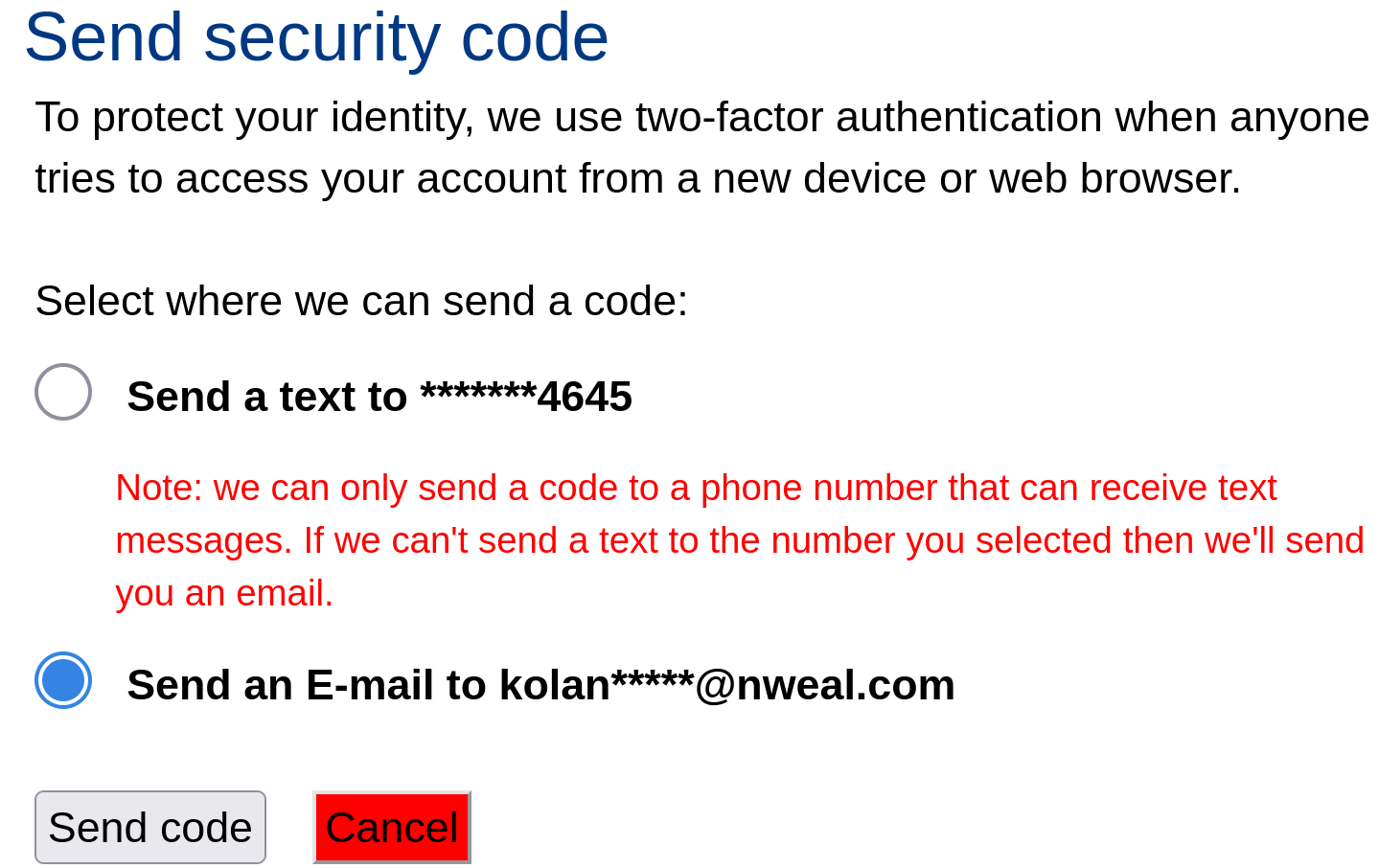
Unfortunately, none of these methods worked. I was sure this 2FA function was vulnerable, but i was curious to explore the user dashboard first then return to the 2FA bypass later. To my surprise, the first thing I noticed in the dashboard was a feature called “Linked Accounts.” This feature allowed users to quickly switch between their accounts by providing the username and password.
I created a second account and used the “Linked Accounts” feature to link it to my primary account, And just by doing this, I was easily able to log in without entering any 2FA code 🙂
Impact
Unauthorized Access: Attackers can easily switch between user accounts without the need for a 2FA code.
Recommended Fix
Require 2FA for Account Switching: Ensure that the “Linked Accounts” function also requires 2FA verification before allowing users to switch accounts.
Conclusion
This 2FA bypass vulnerability highlights a major weakness in the authentication process. While two-factor authentication (2FA) is meant to add an extra layer of security, this flaw completely bypasses it, putting user accounts at risk of unauthorized access.
Final Thoughts:
Hacking and bug bounty hunting aren’t always about using complex codes and payloads. Sometimes, all you need is a hacker’s mindset to creatively exploit the features built by developers.