Introduction : 🔐 Hack WiFi in Morocco
Whether you’re using TP-Link, Inwi Home, WiFi Perso, or even the latest Fibre connections, your network may be vulnerable to cyber attacks. In this post, we expose the exact methods hackers use to hack WiFi in Morocco — and how to protect yourself.

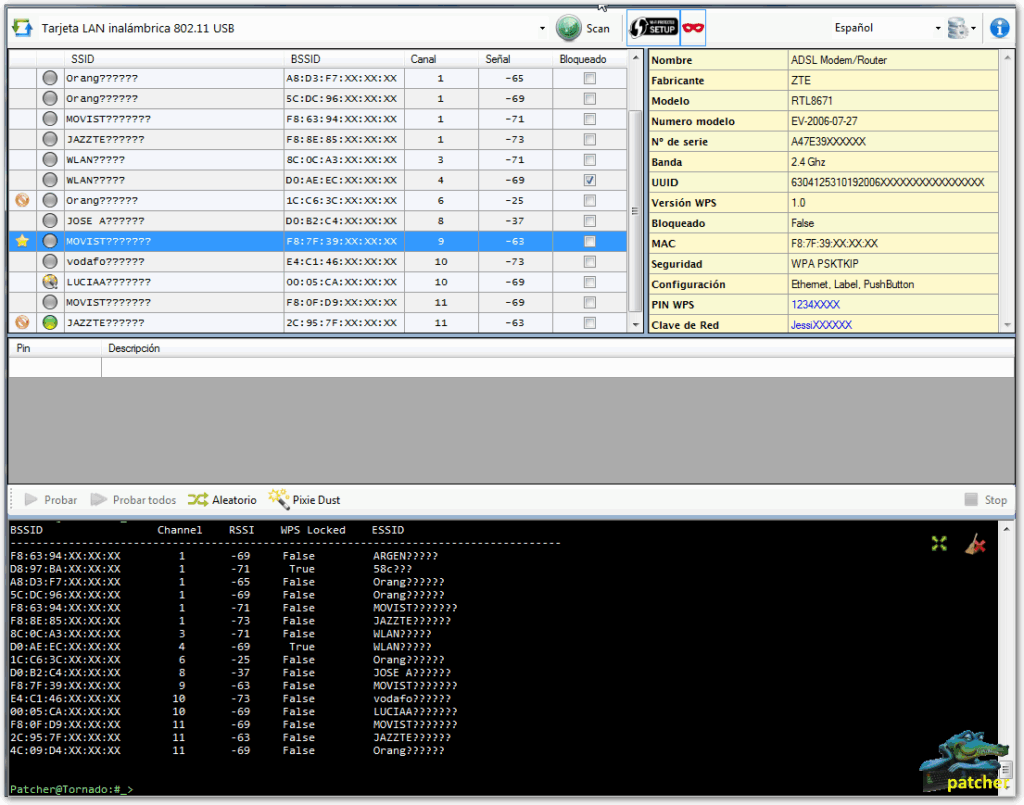
1. 🛑 TP-Link WPS Brute Force Attack
📌 Target: Users with WPS enabled
TP-Link routers often have WPS (Wi-Fi Protected Setup) enabled by default — a feature that allows you to connect via an 8-digit PIN instead of a password.
🧰 Tools used:
- Waircut, Pixie Dust, Wifite, Reaver
⚙️ How it works:
Once the right 8-digit PIN is found, the router gives them the actual WiFi password.
The hacker scans your network to check if WPS is enabled.
They use a script to bruteforce every possible PIN.
🛡️ Protection Tips:
- Access your router settings and disable WPS completely.
- Choose a strong WPA2 or WPA3 password.
2. 🔓 Inwi Home: Handshake Capture & Cracking
📌 Target: Users with default 8-digit passwords (e.g., 45468829)
Most Inwi Home routers come with a simple 8-digit password — easy for brute-force or cracking attacks.
🧰 How hackers do it:
Method 1: Brute-force the password directly
- Use tools like
airmon-ngandwifiteto try thousands of combinations.
Method 2: Capture the Handshake
Here’s how:
- The hacker waits until a device connects to the WiFi or forces a disconnection (deauthentication attack).
- When a device reconnects, the WPA2 handshake is captured using tools like:
airodump-ngbettercaphcxdumptool
- They attempt to crack the handshake:
- Locally: Using
aircrack-ng,hashcat,john the ripper. - In the cloud: Uploading to cracking services like
👉 https://wpa-sec.stanev.org/ (WPA/WPA2 hash audit service)
- Locally: Using
🎯 Goal:
If the password is only 8 digits, it can be cracked in minutes.
🛡️ Protection Tips:
- Change the default password to a long, random mix of characters.
- Example:
G92Kf#94tV#4Lp6QZ! - Avoid using anything based on phone numbers or MAC addresses.
3. 🧱 WiFi Perso: MAC Address as Password
📌 Target: WiFi Perso
“Wifi Perso” default password is set to the MAC address of the router — which is visible to everyone near your house.
📡 How hackers exploit this:
- Using
airodump-ngor any WiFi analyzer, they get your BSSID (MAC address). - If your password is
38:6F:44:XX:XX:XX, they try it directly — or generate variations. - Instant access if it’s a match.
🛡️ Protection Tips:
- Use unique, complex passwords not related to your router or name.
- Example:
L%9gFt#2lWq@8K
4. 🧨 Evil Twin Attack: The Most Dangerous Technique
This method doesn’t require your real password at all.
🧰 Tools used:
Airgeddon,Fluxion,EvilTwin- Portable WiFi dongles (acting as rogue AP)
⚙️ How it works:
- The attacker creates a fake WiFi network with the same name (SSID) as yours.
- Your phone or laptop connects to the fake one thinking it’s legit.
- A fake loghack-wifi-in-morocco/in page appears asking for the password.
- Once entered, it’s sent to the hacker in plain text.
- Some tools even mirror the exact login interface of common routers (Inwi, TP-Link, etc.).
Advanced technique: Captive portal + SSL stripping
- The fake login page can redirect you to an insecure site that collects all your inputs.
🛡️ Protection Tips:
- Always double-check the WiFi you’re connecting to (look for signal strength inconsistency).
- Never enter WiFi passwords on suspicious pop-up pages.
- Use VPN when in public or unknown WiFi zones.
✅ How to Protect Yourself (Quick Summary)
| ✅ Action | 🔐 Why It Matters |
|---|---|
| Disable WPS | Prevent brute-force PIN attacks |
| Change default passwords | Avoid being a victim of dictionary attacks |
| Use strong passwords | Longer passwords take years to crack |
| Monitor your devices | Watch for unknown connections |
| Update router firmware | Close security holes hackers exploit |
| Educate your household | Make sure no one connects to fake WiFi |
🔎 Final Words
If you’re googling “hack Wifi in Morocco” — whether out of curiosity or concern — just know: the best defense is knowledge. Protect your network before someone tests it for you.





